Security in this day and age is critical for your organisation. This article looks at some simple strategies to keeping your server secure from intruders.
Keep all your software up to date
Constant updates every day can be daunting and even annoying for most users, but there is a good reason for them and most of the time they include security updates to keep your systems secure.
Updating is such a simple and effective way to keep all your systems secure, and it is all too often overlooked. It is important to update software on your server as well as all your devices, especially those devices that are used to login to your business systems.
Setup automatic system updates
Did you know that you can configure automatic updates for your server? Here are some great articles that we’ve tried and tested for each operating system:
- CentOS Stream / AlmaLinux – Linuxiac – How to Set up Automatic Updates on Rocky Linux / AlmaLinux
- Debian / Ubuntu – Tecmint – How to Install Security Updates Automatically on Debian and Ubuntu
Don’t want to run automatic updates? Updating your system is really easy. I recommend you install Cockpit for Linux on your system but if you prefer to manually update your system check out these guides instead:
MediaCP Software Updates
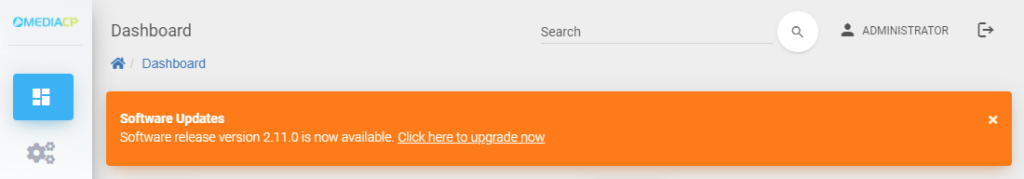
Software updates for the MediaCP are announced on your dashboard so you will always know when a new update is available. Updating the MediaCP software is really easy and involves a single line to complete, however you should always make sure you have a backup before upgrading.
We recommend that you update the MediaCP as soon as an update is available, or at the very least, once every month.
You can update the MediaCP by updating your system packages and running our upgrade utility. You can follow our upgrade guide here: Upgrading – Media Control Panel
Prefer our team to complete this for you? Order an upgrade service instead.
Update your PC
It is just as important to keep your PC updated as it is to keep your system and mediacp up to date. Many intrusions make there way to servers through outdated and unpatched PC’s.
Secure your SSH connection
Here we’ll look at some simple steps to keeping unauthorised users out of your system.
Change the default SSH port
Changing your default SSH port is a very basic level of protection and can help prevent unauthorised acccess, however it does not secure the service; we’ll cover this in the next step.
Important: Make sure to open the new port in your servers firewall before applying changes!
Firewall your SSH port
Many systems come with a firewall already installed, CentOS typically uses firewalld and Debian typically uses ufw. If you have cPanel installed on your system then you might be using ConfigServer Security & Firewall (CSF).
You will need to determine what firewall is running on your system and make sure that you block all connections to port 22 except for your own IP address. If there is no firewall installed then you should really consider installing one. We reccomend using ConfigServer Security & Firewall (CSF) and have a dedicated guide for installing and configuing CSF to work with the Media Control Panel: Setup CSF Firewall
The default SSH port is on 22, however if you have changed the port from 22 then you should replace port 22 with the new port in your firewall command.
Important Note: Before installing any firewall, please check our system requirements to make sure you don’t accidentally block MediaCP services that require internet access.
Disable password login to SSH
Authentication with SSH keys drastically increases the security of your system, especially when password authenticaiton is then disabled.
Step 1 – Generate and install SSH key
- Windows users with Putty: Use SSH Keys with PuTTY on Windows | IONOS DevOps Central
- Mac / Linux users with Terminal: How to disable ssh password login on Linux to increase security – nixCraft (cyberciti.biz)
Step 2 – Disable password login to SSH
After enabling SSH key authentication, it a best practice to disable password authentication. Make sure you’ve tested SSH key login first. If your SSH key doesn’t work, and you disable password login, you’ll lose SSH access.
- Edit /etc/ssh/sshd_config
nano /etc/ssh/sshd_config
- Find this line:
#PasswordAuthentication yes
If the line is commented out with #, remove the # symbol.
- Replace yes with no. The line should look like this when finished:
PasswordAuthentication no
- Restart OpenSSH
systemctl restart sshd.service
Configure Regular Backups
Regular backups don’t necessarily secure your server however they are crucial in order to restore your system if something does go wrong. Hard disk failures are common and without a backup there is no way to recover your data.
Use VPS Snapshots!
If you are using a VPS then you should be using snapshots. If your provider does not include a snapshot feature then you should find another provider!
What are snapshots?
Snapshots allow you to capture and preserve the entire state of a VPS, including it’s data. In the case where something goes wrong, such as a failed upgrade or corrupted data then you can usually restore to the last snapshot within minutes.
Backup the MediaCP and store it offsite
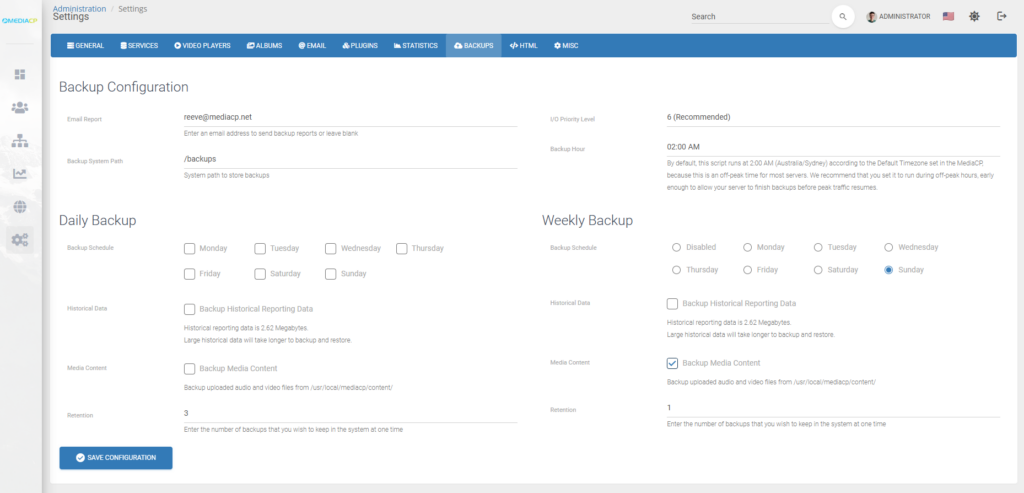
Our software includes a simple and automated backup utility. You should make sure that you have regular backups configured within the MediaCP from Administration -> System Config -> Backups.
We recommend storing backups on a separate disk on your server to protect against disk failure which would result in losing your panel and your backups. If you are using a VPS, you should be able to easily add a new disk to your server to set this up. It is important to ensure the additional disk is large enough to store full backups of your panel and content. This, along with the steps to setup a custom backup path is explained in more detail in our backup documentation: Backup MediaCP
From there for added security you can setup offsite backups by syncing your backups to an offsite location. This could be done by mounting an external cloud drive and storing a copy of your backups there, or by setting up a cronjob that automatically rsync’s or transfers your backups to the external location.